[2022年03月18日]PCCET試験ブレーン問題集で学習注釈と理論
合格させるPalo Alto Networks PCCETテスト練習テスト問題試験問題集
質問 31
Which network firewall operates up to Layer 4 (Transport layer) of the OSI model and maintains information about the communication sessions which have been established between hosts on trusted and untrusted networks?
- A. Static packet-filter
- B. Stateless
- C. Group policy
- D. Stateful
正解: D
質問 32
What does Palo Alto Networks Cortex XDR do first when an endpoint is asked to run an executable?
- A. run a static analysis
- B. run a dynamic analysis
- C. check its execution policy
- D. send the executable to WildFire
正解: C
質問 33
Which endpoint product from Palo Alto Networks can help with SOC visibility?
- A. AutoFocus
- B. STIX
- C. Cortex XDR
- D. WildFire
正解: C
質問 34
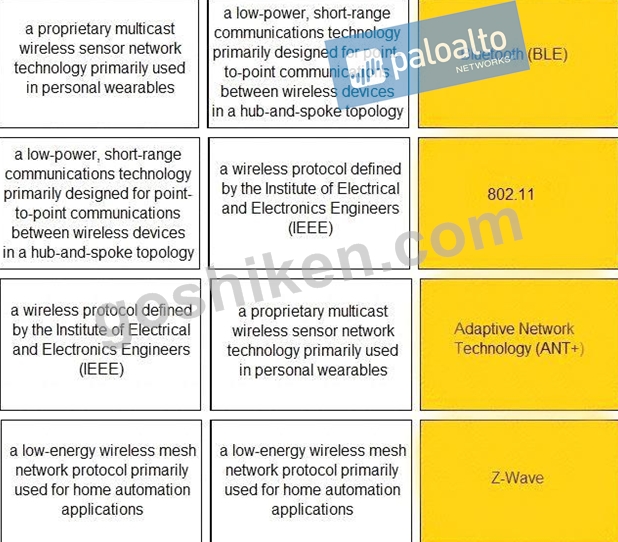
Match the IoT connectivity description with the technology.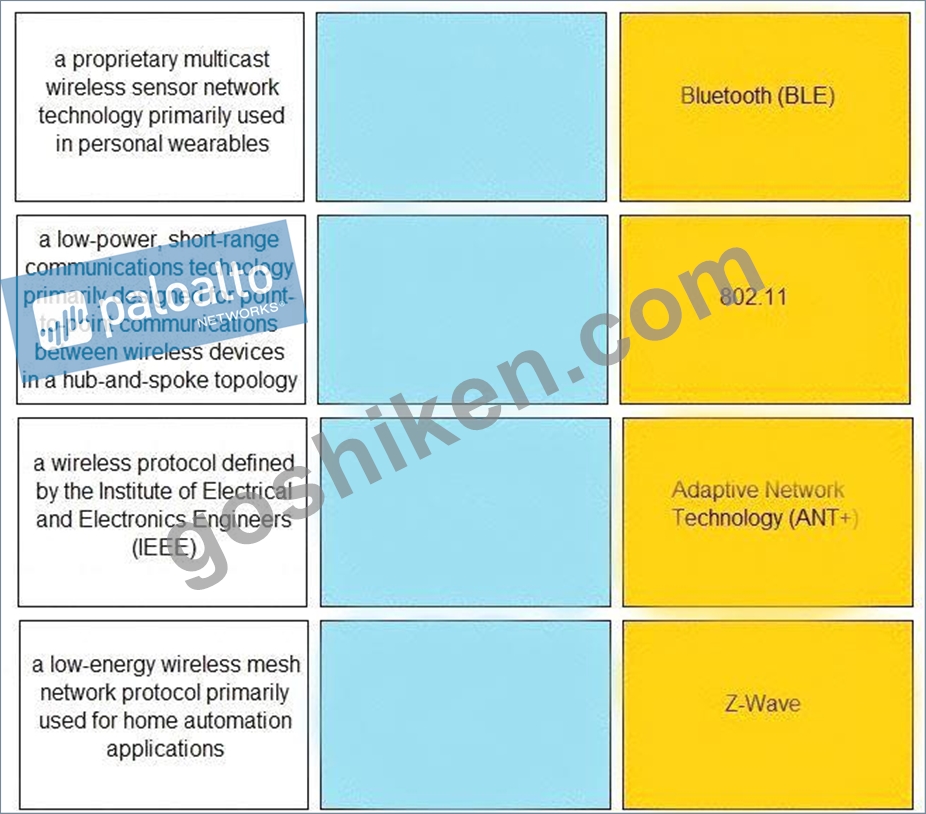
正解:
解説: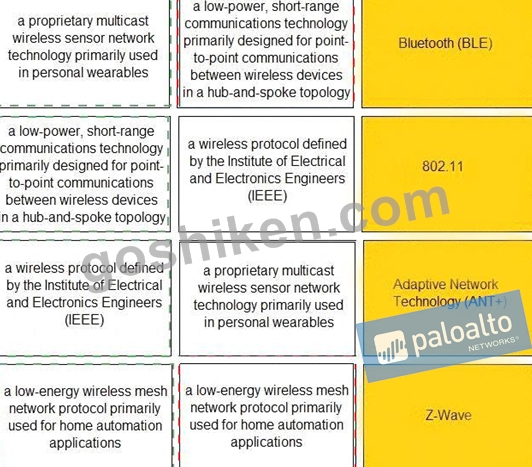
質問 35
Which pillar of Prisma Cloud application security addresses ensuring that your cloud resources and SaaS applications are correctly configured?
- A. compute security
- B. dynamic computing
- C. network protection
- D. visibility, governance, and compliance
正解: D
質問 36
How does DevSecOps improve the Continuous Integration/Continuous Deployment (CI/CD) pipeline?
- A. DevSecOps does security checking after the application code has been processed through the CI/CD pipeline
- B. DevSecOps improves pipeline security by assigning the security team as the lead team for continuous deployment
- C. DevSecOps unites the Security team with the Development and Operations teams to integrate security into the CI/CD pipeline
- D. DevSecOps ensures the pipeline has horizontal intersections for application code deployment
正解: C
質問 37
Which option describes the "selective network security virtualization" phase of incrementally transforming data centers?
- A. during the selective network security virtualization phase, all intra-host traffic is encapsulated and encrypted using the IPSEC protocol
- B. during the selective network security virtualization phase, all intra-host communication paths are strictly controlled
- C. during the selective network security virtualization phase, all intra-host traffic is forwarded to a Web proxy server
- D. during the selective network security virtualization phase, all intra-host traffic is load balanced
正解: B
質問 38
Which type of Wi-Fi attack depends on the victim initiating the connection?
- A. Jasager
- B. Parager
- C. Mirai
- D. Evil twin
正解: A
質問 39
Which item accurately describes a security weakness that is caused by implementing a "ports first" data security solution in a traditional data center?
- A. You may not be able to assign the correct port to your business-critical applications.
- B. You may not be able to open up enough ports for your business-critical applications which will increase the attack surface area.
- C. You may have to open up multiple ports and these ports could also be used to gain unauthorized entry into your datacenter.
- D. You may have to use port numbers greater than 1024 for your business-critical applications.
正解: C
質問 40
Which Palo Alto Networks tools enable a proactive, prevention-based approach to network automation that accelerates security analysis?
- A. AutoFocus
- B. MineMeld
- C. Cortex XDR
- D. WildFire
正解: C
質問 41
Which product from Palo Alto Networks extends the Security Operating Platform with the global threat intelligence and attack context needed to accelerate analysis, forensics, and hunting workflows?
- A. Global Protect
- B. STIX
- C. AutoFocus
- D. WildFire
正解: C
質問 42
How does Prisma SaaS provide protection for Sanctioned SaaS applications?
- A. Prisma SaaS connects to an organizations internal print and file sharing services to provide protection and sharing visibility
- B. Prisma SaaS connects directly to sanctioned external service providers SaaS application service to provide protection and sharing visibility
- C. Prisma access uses Uniform Resource Locator (URL) Web categorization to provide protection and sharing visibility
- D. Prisma SaaS does not provide protection for Sanctioned SaaS applications because they are secure
正解: B
質問 43
Which network analysis tool can be used to record packet captures?
- A. Angry IP Scanner
- B. Netman
- C. Smart IP Scanner
- D. Wireshark
正解: D
質問 44
Which endpoint tool or agent can enact behavior-based protection?
- A. AutoFocus
- B. DNS Security
- C. MineMeld
- D. Cortex XDR
正解: D
解説:
Explanation
質問 45
Which option would be an example of PII that you need to prevent from leaving your enterprise network?
- A. Trade secret
- B. A symmetric encryption key
- C. Credit card number
- D. National security information
正解: C
解説:
Explanation/Reference:
質問 46
In addition to local analysis, what can send unknown files to WildFire for discovery and deeper analysis to rapidly detect potentially unknown malware?
- A. AutoFocus
- B. MineMild
- C. Cortex XDR
- D. Cortex XSOAR
正解: C
質問 47
Which product from Palo Alto Networks enables organizations to prevent successful cyberattacks as well as simplify and strengthen security processes?
- A. AutoFocus
- B. MineMeld
- C. Cortex XDR
- D. Expedition
正解: C
質問 48
Which core component is used to implement a Zero Trust architecture?
- A. VPN Concentrator
- B. Content Identification
- C. Web Application Zone
- D. Segmentation Platform
正解: D
質問 49
What does SIEM stand for?
- A. Security Information and Event Management
- B. Secure Infrastructure and Event Monitoring
- C. Standard Installation and Event Media
- D. Security Infosec and Event Management
正解: A
質問 50
Which attacker profile uses the internet to recruit members to an ideology, to train them, and to spread fear and include panic?
- A. cybercriminals
- B. state-affiliated groups
- C. cyberterrorists
- D. hacktivists
正解: C
質問 51
......
厳密検証されたPCCET問題集と解答でPCCET問題集と正解付き:https://www.goshiken.com/Palo-Alto-Networks/PCCET-mondaishu.html
ベストPaloalto Networks Certification学習ガイドPCCET試験:https://drive.google.com/open?id=1DeY6MDtQseH76RThMDs3FzGnaU0EnkoP
