[2024年01月12日] 無料RHCE EX294公式認定ガイドPDFダウンロード
RedHat EX294公式認定ガイドPDF
RHCE EX294認定を獲得することは、新しい雇用機会とキャリアの進歩につながる可能性のある重要な成果です。 Red Hat Enterprise Linuxは、エンタープライズ環境で広く使用されており、これらのシステムを効果的に管理および管理できる熟練した専門家にとって高い需要があります。 RHCE Ex294試験に合格することにより、候補者は最先端のテクノロジーを操作する能力を実証し、実際の設定で複雑な問題を解決します。
質問 # 14
Create a playbook called packages.yml that:
----------------------------------------------
--> Installs the php and mariadb packages on hosts in the dev, test, and prod host
groups.
--> Installs the Development Tools package group on hosts in the dev host group.
--> Updates all packages to the latest version on hosts in the dev host group.
正解:
解説:
Solution as:
# pwd
home/admin/ansible/
# vim packages.yml
---
- name: Install the packages
hosts: dev,test,prod
vars:
- php_pkg: php
- mariadb_pkg: mariadb
tasks:
- name: install the packages
yum:
name:
- "{{ php_pkg }}"
- "{{ mariadb_pkg }}"
state: latest
- name: install the devops tool packages
hosts: dev
tasks:
- name: install devepment tools
yum:
name: "@Development Tools"
state: latest
- name: upgrade all the packages
yum:
name: "*"
state: latest
exclude: kernel*
!wq
# ansible-playbook package.yml --syntax-check
# ansible-playbook package.yml
質問 # 15
Create a role called sample-apache in /home/sandy/ansible/roles that enables and starts httpd, enables and starts the firewall and allows the webserver service. Create a template called index.html.j2 which creates and serves a message from /var/www/html/index.html Whenever the content of the file changes, restart the webserver service.
Welcome to [FQDN] on [IP]
Replace the FQDN with the fully qualified domain name and IP with the ip address of the node using ansible facts. Lastly, create a playbook in /home/sandy/ansible/ called apache.yml and use the role to serve the index file on webserver hosts.
正解:
解説:
/home/sandy/ansible/apache.yml
/home/sandy/ansible/roles/sample-apache/tasks/main.yml
/home/sandy/ansible/roles/sample-apache/templates/index.html.j2
In /home/sandy/ansible/roles/sample-apache/handlers/main.yml
質問 # 16
Create a role called apache in "/home/admin/ansible/roles" with the following
requirements:
--> The httpd package is installed, enabled on boot, and started.
--> The firewall is enabled and running with a rule to allow access to the web server.
--> template file index.html.j2 is used to create the file /var/www/html/index.html
with the output:
Welcome to HOSTNAME on IPADDRESS
--> Where HOSTNAME is the fqdn of the managed node and IPADDRESS is the IP-Address of
the managed node.
note: you have to create index.html.j2 file.
--> Create a playbook called httpd.yml that uses this role and the playbook runs on
hosts in the webservers host group.
正解:
解説:
Solution as:
----------
# pwd
/home/admin/ansible/roles/
# ansible-galaxy init apache
# vim apache/vars/main.yml
---
# vars file for apache
http_pkg: httpd
firewall_pkg: firewalld
http_srv: httpd
firewall_srv: firewalld
rule: http
webpage: /var/www/html/index.html
template: index.html.j2
:wq!
# vim apache/tasks/package.yml
---
- name: Installing packages
yum:
name:
- "{{http_pkg}}"
- "{{firewall_pkg}}"
state: latest
:wq!
# vim apache/tasks/service.yml
---
- name: start and enable http service
service:
name: "{{http_srv}}"
enabled: true
state: started
- name: start and enable firewall service
service:
name: "{{firewall_srv}}"
enabled: true
state: started
:wq!
# vim apache/tasks/firewall.yml
---
- name: Adding http service to firewall
firewalld:
service: "{{rule}}"
state: enabled
permanent: true
immediate: true
:wq!
# vim apache/tasks/webpage.yml
---
- name: creating template file
template:
src: "{{template}}"
dest: "{{webpage}}"
notify: restart_httpd
!wq
# vim apache/tasks/main.yml
# tasks file for apache
- import_tasks: package.yml
- import_tasks: service.yml
- import_tasks: firewall.yml
- import_tasks: webpage.yml
:wq!
# vim apache/templates/index.html.j2
Welcome to {{ ansible_facts.fqdn }} on {{ ansible_facts.default_ipv4.address }}
# vim apache/handlers/main.yml
---
# handlers file for apache
- name: restart_httpd
service:
name: httpd
state: restarted
:wq!
# cd ..
# pwd
/home/admin/ansible/
# vim httpd.yml
---
- name: Including apache role
hosts: webservers
pre_tasks:
- name: pretask message
debug:
msg: 'Ensure webserver configuration'
roles:
- ./roles/apache
post_tasks:
- name: Check webserver
uri:
url: "http://{{ ansible_facts.default_ipv4.address }}"
return_content: yes
status_code: 200
:wq!
# ansible-playbook httpd.yml --syntax-check
# ansible-playbook httpd.yml
# curl http://serverx
質問 # 17
Create a playbook called regulartasks.yml which has the system that append the date to /root/datefile every day at noon. Name is job 'datejob'
正解:
解説:
Solution as:
質問 # 18
Install the RHEL system roles package and create a playbook called timesync.yml that:
--> Runs over all managed hosts.
--> Uses the timesync role.
--> Configures the role to use the time server 192.168.10.254 ( Hear in redhat lab
use "classroom.example.com" )
--> Configures the role to set the iburst parameter as enabled.
正解:
解説:
Solution as:
# pwd
home/admin/ansible/
# sudo yum install rhel-system-roles.noarch -y
# cd roles/
# ansible-galaxy list
# cp -r /usr/share/ansible/roles/rhelsystem-roles.timesync .
# vim timesync.yml
---
- name: timesynchronization
hosts: all
vars:
timesync_ntp_provider: chrony
timesync_ntp_servers:
- hostname: classroom.example.com _ in exam its ip-address
iburst: yes
timezone: Asia/Kolkata
roles:
- rhel-system-roles.timesync
tasks:
- name: set timezone
timezone:
name: "{{ timezone }}"
:wq!
timedatectl list-timezones | grep india
# ansible-playbook timesync.yml --syntax-check
# ansible-playbook timesync.yml
# ansible all -m shell -a 'chronyc sources -v'
# ansible all -m shell -a 'timedatectl'
# ansible all -m shell -a 'systemctl is-enabled chronyd'
質問 # 19
Install and configure ansible
User sandy has been created on your control node with the appropriate permissions already, do not change or modify ssh keys. Install the necessary packages to run ansible on the control node. Configure ansible.cfg to be in folder /home/sandy/ansible/ansible.cfg and configure to access remote machines via the sandy user. All roles should be in the path /home/sandy/ansible/roles. The inventory path should be in /home/sandy/ansible/invenlory.
You will have access to 5 nodes.
node1.example.com
node2.example.com
node3.example.com
node4.example.com
node5.example.com
Configure these nodes to be in an inventory file where node I is a member of group dev. nodc2 is a member of group test, node3 is a member of group proxy, nodc4 and node 5 are members of group prod. Also, prod is a member of group webservers.
正解:
解説:
In/home/sandy/ansible/ansible.cfg
[defaults]
inventory=/home/sandy/ansible/inventory
roles_path=/home/sandy/ansible/roles
remote_user= sandy
host_key_checking=false
[privilegeescalation]
become=true
become_user=root
become_method=sudo
become_ask_pass=false
In /home/sandy/ansible/inventory
[dev]
node 1 .example.com
[test]
node2.example.com
[proxy]
node3 .example.com
[prod]
node4.example.com
node5 .example.com
[webservers:children]
prod
質問 # 20
Use Ansible Galaxy with a requirements file called /home/admin/ansible/roles/
install.yml to download and install roles to /home/admin/ansible/roles from the
following URLs:
http:// classroom.example.com /role1.tar.gz The name of this role should be balancer
http:// classroom.example.com /role2.tar.gz The name of this role should be phphello
正解:
解説:
Solution as:
# pwd
/home/admin/ansible/roles
# vim install.yml
---
- src: http://classroom.example.com/role1.tar.gz
name: balancer
- src: http://classroom.example.com/role2.tar.gz
name: phphello
:wq!
# pwd
/home/admin/ansible
# ansible-galaxy install -r roles/install.yml -p roles
質問 # 21
Create a playbook called timesvnc.yml in /home/sandy/ansible using rhel system role timesync. Set the time to use currently configured nip with the server 0.uk.pool.ntp.org. Enable burst. Do this on all hosts.
- A. Solution as:

- B. Solution as:

正解:B
質問 # 22
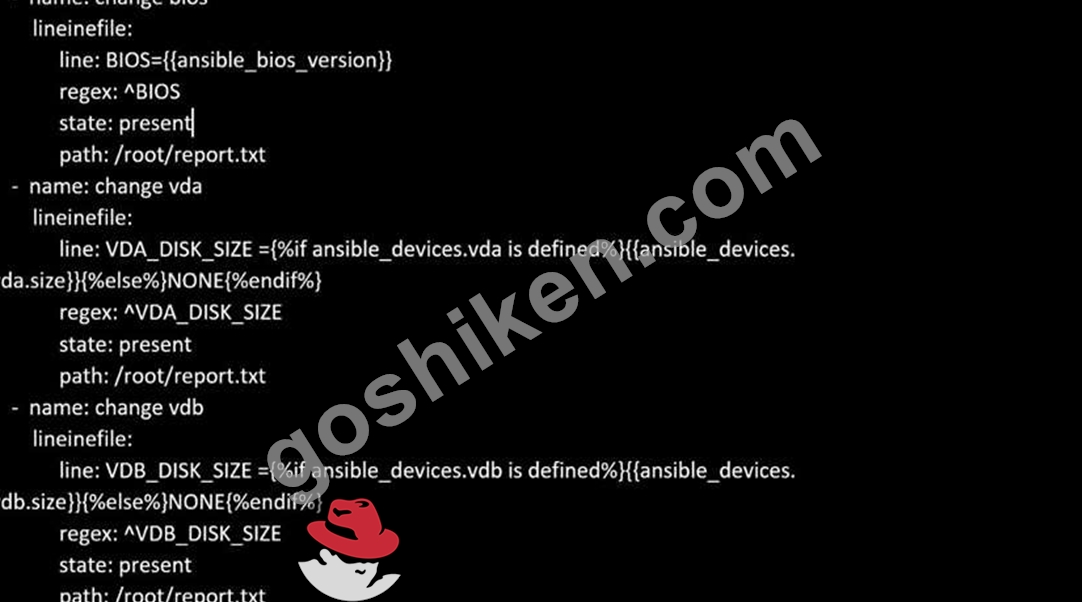
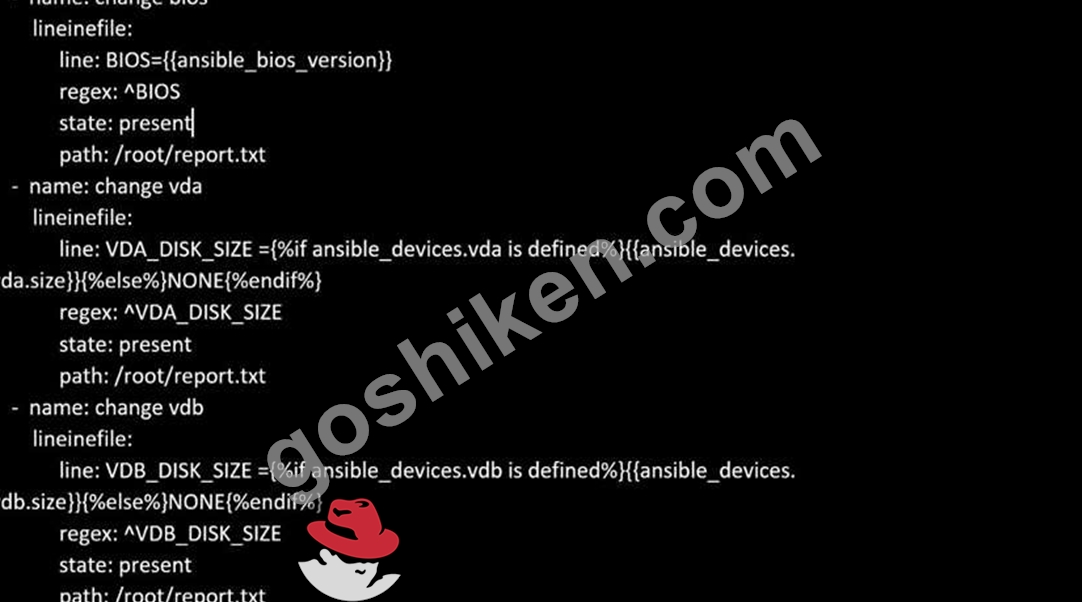
Create a file in /home/sandy/ansible/ called report.yml. Using this playbook, get a file called report.txt (make it look exactly as below). Copy this file over to all remote hosts at /root/report.txt. Then edit the lines in the file to provide the real information of the hosts. If a disk does not exist then write NONE.
正解:
解説:
Solution as: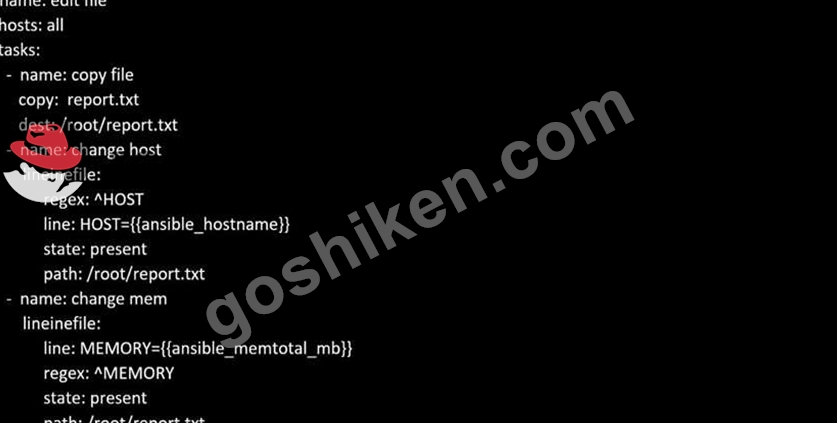
質問 # 23
Create a file called requirements.yml in /home/sandy/ansible/roles to install two roles. The source for the first role is geerlingguy.haproxy and geerlingguy.php. Name the first haproxy-role and the second php-role. The roles should be installed in /home/sandy/ansible/roles.
- A. in /home/sandy/ansible/roles
vim requirements.yml
Run the requirements file from the roles directory:
ansible-galaxy install -r requirements.yml -p /home/sandy/ansible/roles - B. in /home/sandy/ansible/roles
vim requirements.yml
Run the requirements file from the roles directory:
ansible-galaxy install -r requirements.yml -p /home/sandy/ansible/roles
正解:A
質問 # 24
Create a playbook called timesvnc.yml in /home/sandy/ansible using rhel system role timesync. Set the time to use currently configured nip with the server 0.uk.pool.ntp.org. Enable burst. Do this on all hosts.
正解:
解説:
Solution as:
質問 # 25
Create an empty encrypted file called myvault.yml in /home/sandy/ansible and set the password to notsafepw. Rekey the password to iwejfj2221.
正解:
解説:
ansible-vault create myvault.yml
Create new password: notsafepw Confirm password: notsafepw ansible-vault rekey myvault.yml
Current password: notsafepw New password: iwejfj2221 Confirm password: iwejfj2221
質問 # 26
Create the users in the file usersjist.yml file provided. Do this in a playbook called users.yml located at /home/sandy/ansible. The passwords for these users should be set using the lock.yml file from TASK7. When running the playbook, the lock.yml file should be unlocked with secret.txt file from TASK 7.
All users with the job of 'developer' should be created on the dev hosts, add them to the group devops, their password should be set using the pw_dev variable. Likewise create users with the job of 'manager' on the proxy host and add the users to the group 'managers', their password should be set using the pw_mgr variable.
正解:
解説:
ansible-playbook users.yml -vault-password-file=secret.txt
質問 # 27
Create a file called adhoc.sh in /home/sandy/ansible which will use adhoc commands to set up a new repository.
The name of the repo will be 'EPEL' the description 'RHEL8' the baseurl is 'https://dl.fedoraproject.org/pub/epel/epel-release-latest-8.noarch.rmp' there is no gpgcheck, but you should enable the repo.
* You should be able to use an bash script using adhoc commands to enable repos.
Depending on your lab setup, you may need to make this repo "state=absent" after you pass this task.
正解:
解説:
chmod 0777 adhoc.sh
vim adhoc.sh
#I/bin/bash
ansible all -m yum_repository -a 'name=EPEL description=RHEL8
baseurl=https://dl.fedoraproject.org/pub/epel/epel-release-latest-8.noarch.rmp
gpgcheck=no enabled=yes'
質問 # 28
Create a file called specs.empty in home/bob/ansible on the local machine as follows:
HOST=
MEMORY=
BIOS=
VDA_DISK_SIZE=
VDB_DISK_SIZE=
Create the playbook /home/bob/ansible/specs.yml which copies specs.empty to all remote nodes' path /root/specs.txt. Using the specs.yml playbook then edit specs.txt on the remote machines to reflect the appropriate ansible facts.
正解:
解説:
Solution as: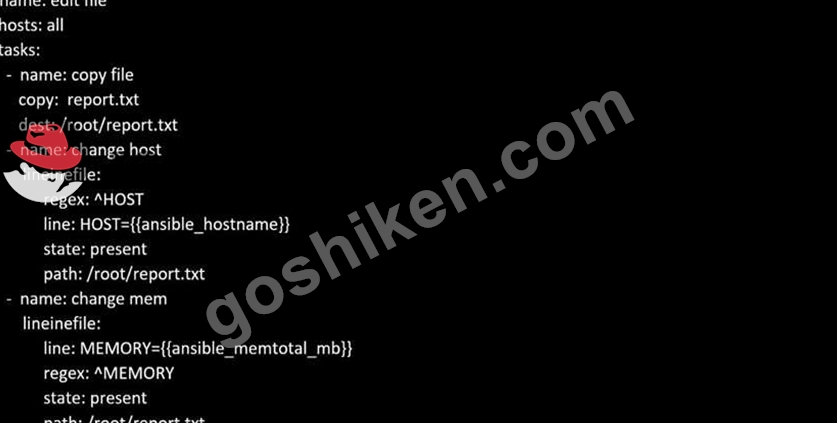
質問 # 29
Create a jinja template in /home/sandy/ansible/ and name it hosts.j2. Edit this file so it looks like the one below. The order of the nodes doesn't matter. Then create a playbook in /home/sandy/ansible called hosts.yml and install the template on dev node at /root/myhosts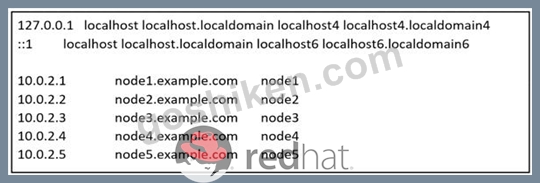
正解:
解説:
Solution as:
質問 # 30
Create a file called packages.yml in /home/sandy/ansible to install some packages for the following hosts. On dev, prod and webservers install packages httpd, mod_ssl, and mariadb. On dev only install the development tools package. Also, on dev host update all the packages to the latest.
- A. Option
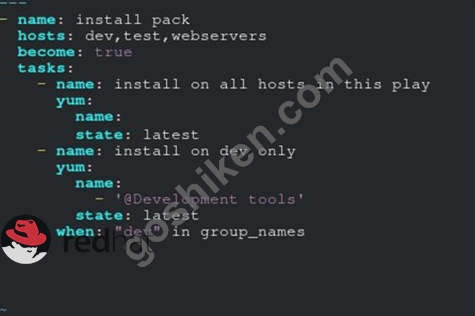
** NOTE 1 a more acceptable answer is likely 'present' since it's not asking to install the latest state: present
** NOTE 2 need to update the development node
- name: update all packages on development node
yum:
name: '*'
state: latest - B. Option

** NOTE 1 a more acceptable answer is likely 'present' since it's not asking to install the latest state: present
** NOTE 2 need to update the development node
- name: update all packages on development node
yum:
name: '*'
state: latest
正解:B
質問 # 31
Create an ansible vault password file called lock.yml with the password reallysafepw in the /home/sandy/ansible directory. In the lock.yml file define two variables. One is pw_dev and the password is 'dev' and the other is pw_mgr and the password is 'mgr' Create a regular file called secret.txt which contains the password for lock.yml.
正解:
解説:
ansible-vault create lock.yml
New Vault Password: reallysafepw
Confirm: reallysafepw
質問 # 32
Create a playbook called web.yml as follows:
* The playbook runs on managed nodes in the "dev" host group
* Create the directory /webdev with the following requirements:
--> membership in the apache group
--> regular permissions: owner=r+w+execute, group=r+w+execute, other=r+execute
s.p=set group-id
* Symbolically link /var/www/html/webdev to /webdev
* Create the file /webdev/index.html with a single line of text that reads:
"Development"
--> it should be available on http://servera.lab.example.com/webdev/index.html
正解:
解説:
Solution as:
# pwd
/home/admin/ansible/
# vim web.yml
---
- name:
hosts: dev
tasks:
- name: create group
yum:
name: httpd
state: latest
- name: create group
group:
name: apache
state: present
- name: creating directiory
file:
path: /webdev
state: directory
mode: '2775'
group: apache
- sefcontext:
target: '/webdev/index.html'
setype: httpd_sys_content_t
state: present
- name: Apply new SELinux file context to filesystem
command: restorecon -irv
- name: creating symbolic link
file:
src: /webdev
dest: /var/www/html/webdev
state: link
force: yes
- name: creating file
file:
path: /webdev/index.html
sate: touch
- name: Adding content to index.html file
copy:
dest: /webdev/index.html
content: "Development"
- name: add service to the firewall
firewalld:
service: http
permanent: yes
state: enabled
immediate: yes
- name: active http service
service:
name: httpd
state: restarted
enabled: yes
:wq
# ansible-playbook web.yml --syntax-check
# ansible-playbook web.yml
質問 # 33
Create a playbook /home/bob /ansible/motd.yml that runs on all inventory hosts and docs the following: The playbook should replaee any existing content of/etc/motd in the following text. Use ansible facts to display the FQDN of each host On hosts in the dev host group the line should be "Welcome to Dev Server FQDN".
On hosts in the webserver host group the line should be "Welcome to Apache Server FQDN".
On hosts in the database host group the line should be "Welcome to MySQL Server FQDN".
- A. /home/sandy/ansible/apache.yml

/home/sandy/ansible/roles/sample-apache/tasks/main.yml - B. /home/sandy/ansible/apache.yml

/home/sandy/ansible/roles/sample-apache/tasks/main.yml
正解:B
質問 # 34
Create a file called packages.yml in /home/sandy/ansible to install some packages for the following hosts. On dev, prod and webservers install packages httpd, mod_ssl, and mariadb. On dev only install the development tools package. Also, on dev host update all the packages to the latest.
正解:
解説:
Solution as:
** NOTE 1 a more acceptable answer is likely 'present' since it's not asking to install the latest
state: present
** NOTE 2 need to update the development node
- name: update all packages on development node
yum:
name: '*'
state: latest
質問 # 35
......
無料EX294試験問題集試験点数を伸ばそう:https://www.goshiken.com/RedHat/EX294-mondaishu.html
