無料で使えるEX294試験ブレーン問題集認定ガイド問題と解答
EX294認定概要最新のEX294のPDF問題集
Redhat Ex294認定試験は、RHCE試験の最新バージョンであり、Red Hat Enterprise Linux 8 Systemsの管理と構成に必要なスキルに焦点を当てています。この試験は、システム管理、ネットワーク管理、セキュリティ、自動化などの分野の専門家の知識とスキルをテストするように設計されています。この認定は、Red HatのOpenShiftコンテナプラットフォームを使用して、候補者が仮想マシンとコンテナを展開および管理する機能を検証します。全体として、Redhat Ex294認定は、Red Hat Enterprise Linux 8 Systemsの管理と構成に関する専門知識を実証したいITプロフェッショナルにとって貴重な資産です。
RedHat EX294試験に合格することは、Linuxシステム管理でキャリアアップを目指すITプロフェッショナルにとって重要な成果です。この認定は、RHEL 8システムの管理に関する知識とスキルを検証するだけでなく、プロフェッショナルな成長への取り組みと、RHEL 8を使用する組織のニーズに応える能力を示すものです。また、RHCEの認定を取得することは、Linuxシステム管理分野でのITプロフェッショナルの給与水準を上げ、より多くの仕事の機会をもたらすことができます。
質問 # 12
In /home/sandy/ansible/ create a playbook called logvol.yml. In the play create a logical volume called Iv0 and make it of size 1500MiB on volume group vgO If there is not enough space in the volume group print a message "Not enough space for logical volume" and then make a 800MiB Iv0 instead. If the volume group still doesn't exist, create a message "Volume group doesn't exist" Create an xfs filesystem on all Iv0 logical volumes. Don't mount the logical volume.
正解:
解説:
Solution as: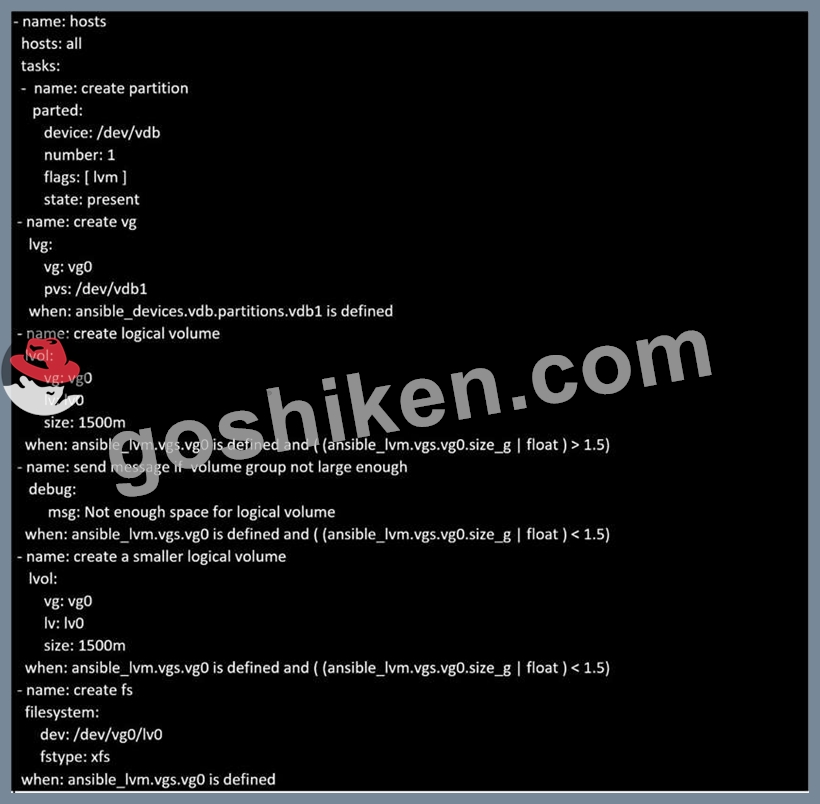
Topic 1, LAB SETUP
You will need to set up your lab by creating 5 managed nodes and one control node.
So 6 machines total. Download the free RHEL8 iso from Red Hat Developers website.
***Control node you need to set up***
You need to create some static ips on your managed nodes then on the control node set them up in the
/etc/hosts file as follows:
vim /etc/hosts
10.0.2.21 node1.example.com
10.0.2.22 node2.example.com
10.0.2.23 node3.example.com
10.0.2.24 node4.example.com
10.0.2.25 node5.example.com
yum -y install ansible
useradd ansible
echo password | passwd --stdin ansible
echo "ansible ALL=(ALL) NOPASSWD:ALL
su - ansible; ssh-keygen
ssh-copy-id node1.example.com
ssh-copy-id node2.example.com
ssh-copy-id node3.example.com
ssh-copy-id node4.example.com
ssh-copy-id node5.example.com
***Each manage node setup***
First, add an extra 2GB virtual harddisk to each control node 1,2,3. Then add an extra hard disk to control
node 4. Do not add an extra hard disk to node 5. When you start up these machines the extra disks should be
automatically located at /dev/sdb (or /dev/vdb depending on your hypervisor).
useradd ansible
echo password | passwd --stdin ansible
echo "ansible ALL=(ALL) NOPASSWD:ALL" > /etc/sudoers.d/ansible
Note python3 should be installed by default, however if it is not then on both the control node and managed
nodes you can install it also set the default python3 if you are having trouble with python2 being the default.
yum -y install python3
alternatives --set python /usr/bin/python3
All machines need the repos available. You did this in RHSCA. To set up locally you just need to do the same
for each machine. Attach the rhel8 iso as a disk to virtualbox, kvm or whatever hypervisor you are using (this
will be /dev/sr0). Then inside the machine:
mount /dev/sr0 to /mnt
Then you will have all the files from the iso in /mnt.
mkdir /repo
cp -r /mnt /repo
vim /etc/yum.repos.d/base.repo
Inside this file:
[baseos]
name=baseos
baseurl=file:///repo/BaseOS
gpgcheck=0
Also the appstream
vim /etc/yum.repos.d/appstream.repo
Inside this file:
[appstream]
name=appstream
baseurl=file:///repo/AppStream
gpgcheck=0
質問 # 13
Create a file called requirements.yml in /home/sandy/ansible/roles to install two roles. The source for the first role is geerlingguy.haproxy and geerlingguy.php. Name the first haproxy-role and the second php-role. The roles should be installed in /home/sandy/ansible/roles.
正解:
解説:
in /home/sandy/ansible/roles
vim requirements.yml
Run the requirements file from the roles directory:
ansible-galaxy install -r requirements.yml -p /home/sandy/ansible/roles
質問 # 14
Create a role called sample-apache in /home/sandy/ansible/roles that enables and starts httpd, enables and starts the firewall and allows the webserver service. Create a template called index.html.j2 which creates and serves a message from /var/www/html/index.html Whenever the content of the file changes, restart the webserver service.
Welcome to [FQDN] on [IP]
Replace the FQDN with the fully qualified domain name and IP with the ip address of the node using ansible facts. Lastly, create a playbook in /home/sandy/ansible/ called apache.yml and use the role to serve the index file on webserver hosts.
- A. Option

/home/sandy/ansible/roles/sample-apache/tasks/main.yml
/home/sandy/ansible/roles/sample-apache/templates/index.html.j2
In /home/sandy/ansible/roles/sample-apache/handlers/main.yml
- B. Option

/home/sandy/ansible/roles/sample-apache/tasks/main.yml
/home/sandy/ansible/roles/sample-apache/templates/index.html.j2
In /home/sandy/ansible/roles/sample-apache/handlers/main.yml
正解:A
質問 # 15
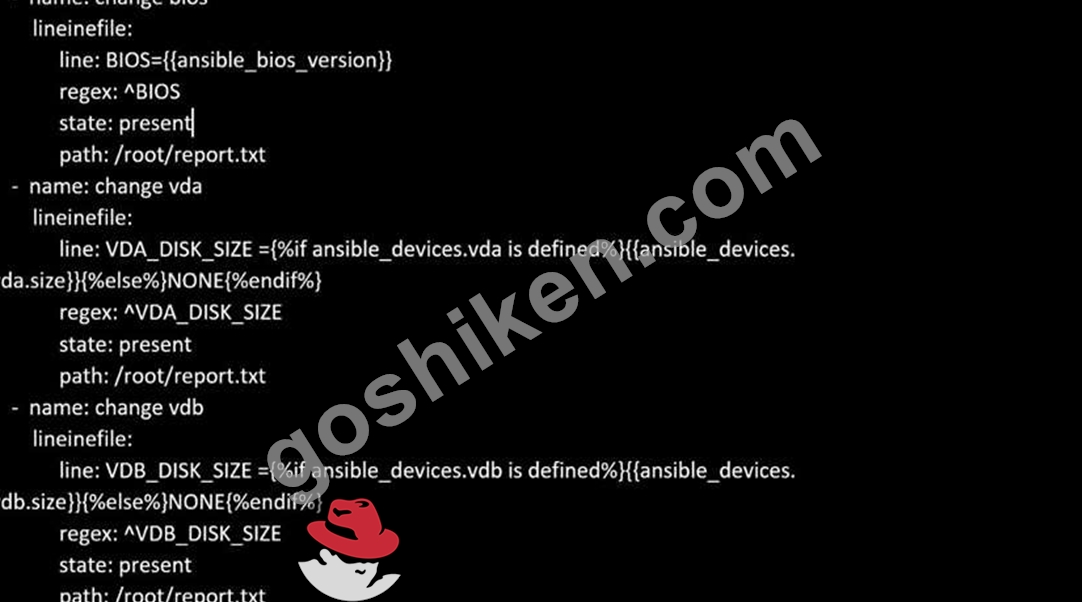
Create a file called specs.empty in home/bob/ansible on the local machine as follows:
HOST=
MEMORY=
BIOS=
VDA_DISK_SIZE=
VDB_DISK_SIZE=
Create the playbook /home/bob/ansible/specs.yml which copies specs.empty to all remote nodes' path /root/specs.txt. Using the specs.yml playbook then edit specs.txt on the remote machines to reflect the appropriate ansible facts.
正解:
解説:
Solution as: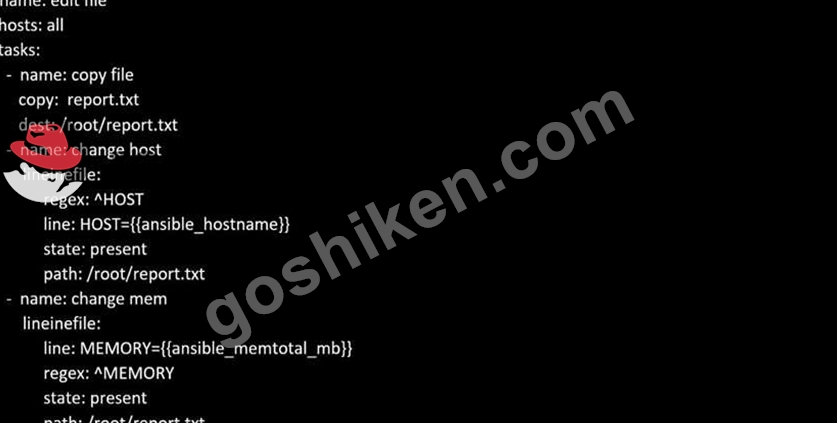
質問 # 16
Install and configure Ansible on the control-node control.realmX.example.com as
follows:
-------------------------------------------------------------------------------------------
--> Install the required packages
--> Create a static inventory file called /home/admin/ansible/inventory as follows:
node1.realmX.example.com is a member of the dev host group
node2.realmX.example.com is a member of the test host group
node3.realmX.example.com & node4.realmX.example.com are members of the prod
host group
node5.realmX.example.com is a member of the balancers host group.
prod group is a member of the webservers host group
--> Create a configuration file called ansible.cfg as follows:
--> The host inventory file /home/admin/ansible/inventory is defined
--> The location of roles used in playbooks is defined as /home/admin/ansible/ roles
正解:
解説:
Solution as:
Through physical host, login to workstation.lab.example.com with user root.
# ssh [email protected]
# hostname
workstation.lab.example.com
# yum install platform-python*
# su - admin
# pwd
/home/admin/
# vim .vimrc
# mkdir -p ansible/roles
# cd ansible
# vim inventory
[dev]
servera.lab.example.com
[test]
serverb.example.com
[prod]
serverc.example.com
serverd.example.com
[balancer]
serverd.lab.example.com
[webservers:children]
prod
:!wq
# vim ansible.cfg
[defaults]
inventory = ./inventory
role_path = ./roles
remote_user = admin
ask_pass = false
[privilege_escalation]
become = true
become_method = sudo
become_user = root
become_ask_pass = false
:!wq
# ansible all --list-hosts
質問 # 17
Create a playbook /home/bob /ansible/motd.yml that runs on all inventory hosts and docs the following: The playbook should replaee any existing content of/etc/motd in the following text. Use ansible facts to display the FQDN of each host On hosts in the dev host group the line should be "Welcome to Dev Server FQDN".
On hosts in the webserver host group the line should be "Welcome to Apache Server FQDN".
On hosts in the database host group the line should be "Welcome to MySQL Server FQDN".
- A. /home/sandy/ansible/apache.yml

/home/sandy/ansible/roles/sample-apache/tasks/main.yml - B. /home/sandy/ansible/apache.yml

/home/sandy/ansible/roles/sample-apache/tasks/main.yml
正解:B
質問 # 18
Create a playbook called issue.yml in /home/sandy/ansible which changes the file /etc/issue on all managed nodes: If host is a member of (lev then write "Development" If host is a member of test then write "Test" If host is a member of prod then write "Production"
- A. Solution as:
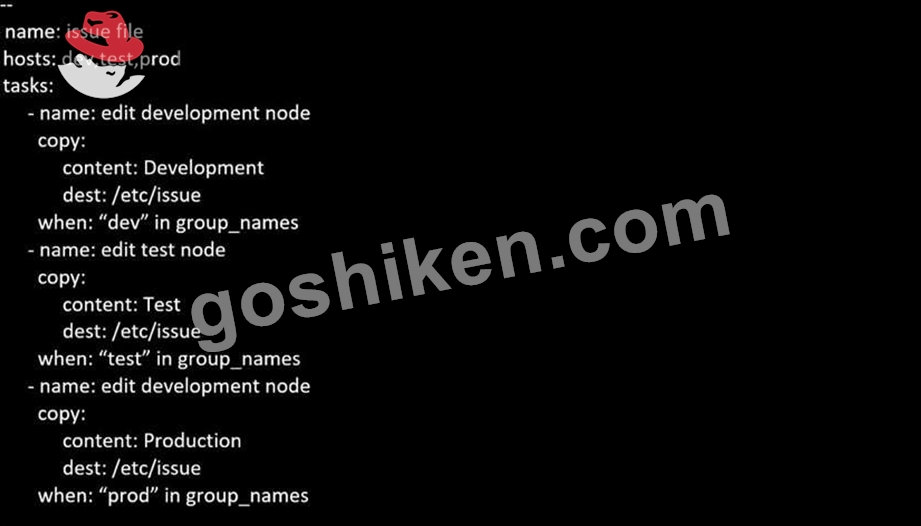
- B. Solution as:

正解:A
質問 # 19
Create the users in the file usersjist.yml file provided. Do this in a playbook called users.yml located at /home/sandy/ansible. The passwords for these users should be set using the lock.yml file from TASK7. When running the playbook, the lock.yml file should be unlocked with secret.txt file from TASK 7.
All users with the job of 'developer' should be created on the dev hosts, add them to the group devops, their password should be set using the pw_dev variable. Likewise create users with the job of 'manager' on the proxy host and add the users to the group 'managers', their password should be set using the pw_mgr variable.
- A. ansible-playbook users.yml -vault-password-file=secret.txt

- B. ansible-playbook users.yml -vault-password-file=secret.txt

正解:B
質問 # 20
Create the users in the file usersjist.yml file provided. Do this in a playbook called users.yml located at /home/sandy/ansible. The passwords for these users should be set using the lock.yml file from TASK7. When running the playbook, the lock.yml file should be unlocked with secret.txt file from TASK 7.
All users with the job of 'developer' should be created on the dev hosts, add them to the group devops, their password should be set using the pw_dev variable. Likewise create users with the job of 'manager' on the proxy host and add the users to the group 'managers', their password should be set using the pw_mgr variable.
正解:
解説:
ansible-playbook users.yml -vault-password-file=secret.txt
質問 # 21
Create a file called specs.empty in home/bob/ansible on the local machine as follows:
HOST=
MEMORY=
BIOS=
VDA_DISK_SIZE=
VDB_DISK_SIZE=
Create the playbook /home/bob/ansible/specs.yml which copies specs.empty to all remote nodes' path /root/specs.txt. Using the specs.yml playbook then edit specs.txt on the remote machines to reflect the appropriate ansible facts.
- A. Solution as:

- B. Solution as:
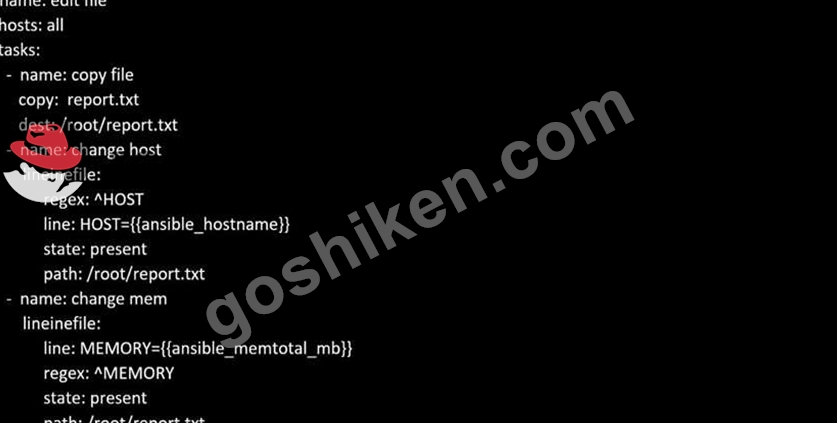
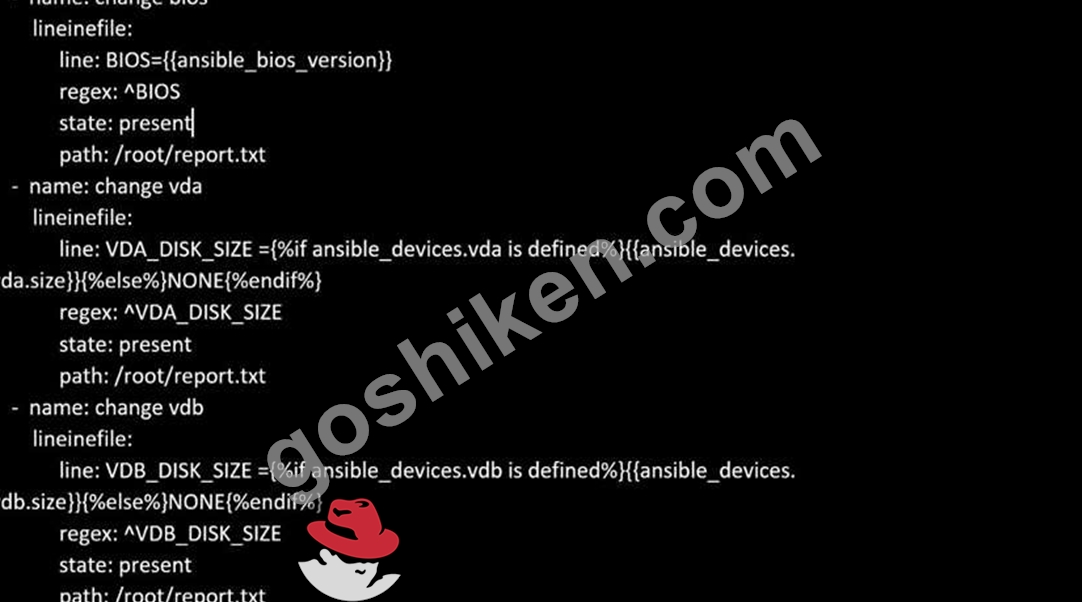
正解:A
質問 # 22
Create a playbook called webdev.yml in 'home/sandy/ansible. The playbook will create a directory Avcbdev on dev host. The permission of the directory are 2755 and owner is webdev. Create a symbolic link from /Webdev to /var/www/html/webdev. Serve a file from Avebdev7index.html which displays the text "Development" Curl http://node1.example.com/webdev/index.html to test
- A. Solution as:
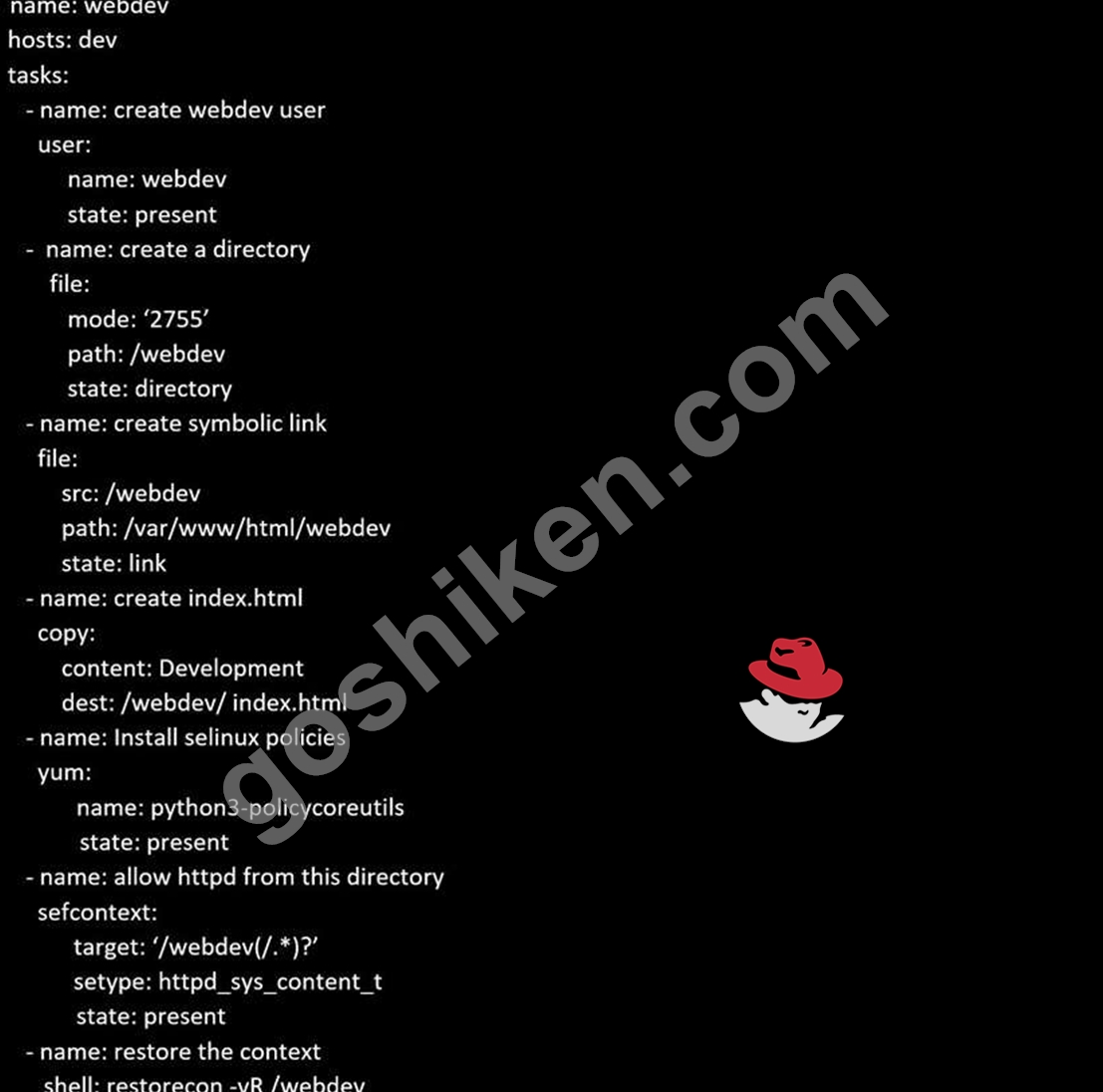
- B. Solution as:
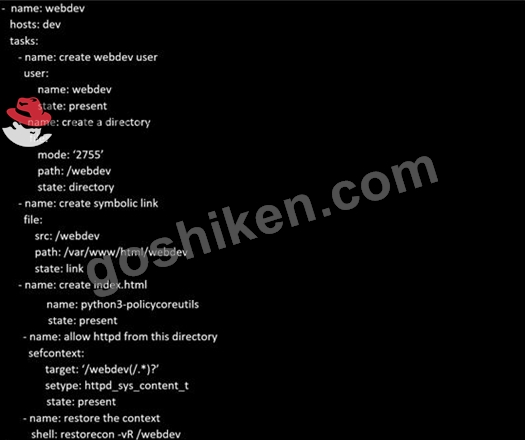
正解:A
質問 # 23
Modify file content.
------------------------
Create a playbook called /home/admin/ansible/modify.yml as follows:
* The playbook runs on all inventory hosts
* The playbook replaces the contents of /etc/issue with a single line of text as
follows:
--> On hosts in the dev host group, the line reads: "Development"
--> On hosts in the test host group, the line reads: "Test"
--> On hosts in the prod host group, the line reads: "Production"
正解:
解説:
Solution as:
# pwd
/home/admin/ansible
# vim modify.yml
---
- name:
hosts: all
tasks:
- name:
copy:
content: "Development"
dest: /etc/issue
when: inventory_hostname in groups['dev']
- name:
copy:
content: "Test"
dest: /etc/issue
when: inventory_hostname in groups['test']
- name:
copy:
content: "Production"
dest: /etc/issue
when: inventory_hostname in groups['prod']
:wq
# ansible-playbook modify.yml --syntax-check
# ansible-playbook modify.yml
質問 # 24
Create a playbook called timesvnc.yml in /home/sandy/ansible using rhel system role timesync. Set the time to use currently configured nip with the server 0.uk.pool.ntp.org. Enable burst. Do this on all hosts.
- A. Solution as:

- B. Solution as:

正解:A
質問 # 25
Create a file called requirements.yml in /home/sandy/ansible/roles to install two roles. The source for the first role is geerlingguy.haproxy and geerlingguy.php. Name the first haproxy-role and the second php-role. The roles should be installed in /home/sandy/ansible/roles.
- A. in /home/sandy/ansible/roles
vim requirements.yml
Run the requirements file from the roles directory:
ansible-galaxy install -r requirements.yml -p /home/sandy/ansible/roles - B. in /home/sandy/ansible/roles
vim requirements.yml
Run the requirements file from the roles directory:
ansible-galaxy install -r requirements.yml -p /home/sandy/ansible/roles
正解:A
質問 # 26
Create a jinja template in /home/sandy/ansible/ and name it hosts.j2. Edit this file so it looks like the one below. The order of the nodes doesn't matter. Then create a playbook in /home/sandy/ansible called hosts.yml and install the template on dev node at /root/myhosts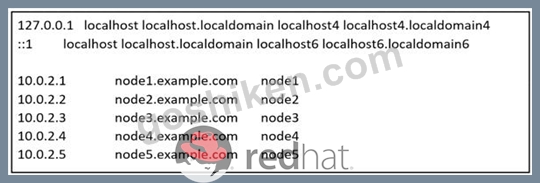
- A. Solution as:

- B. Solution as:

正解:B
質問 # 27
Create a playbook called webdev.yml in 'home/sandy/ansible. The playbook will create a directory Avcbdev on dev host. The permission of the directory are 2755 and owner is webdev. Create a symbolic link from /Webdev to /var/www/html/webdev. Serve a file from Avebdev7index.html which displays the text "Development" Curl http://node1.example.com/webdev/index.html to test
正解:
解説:
Solution as: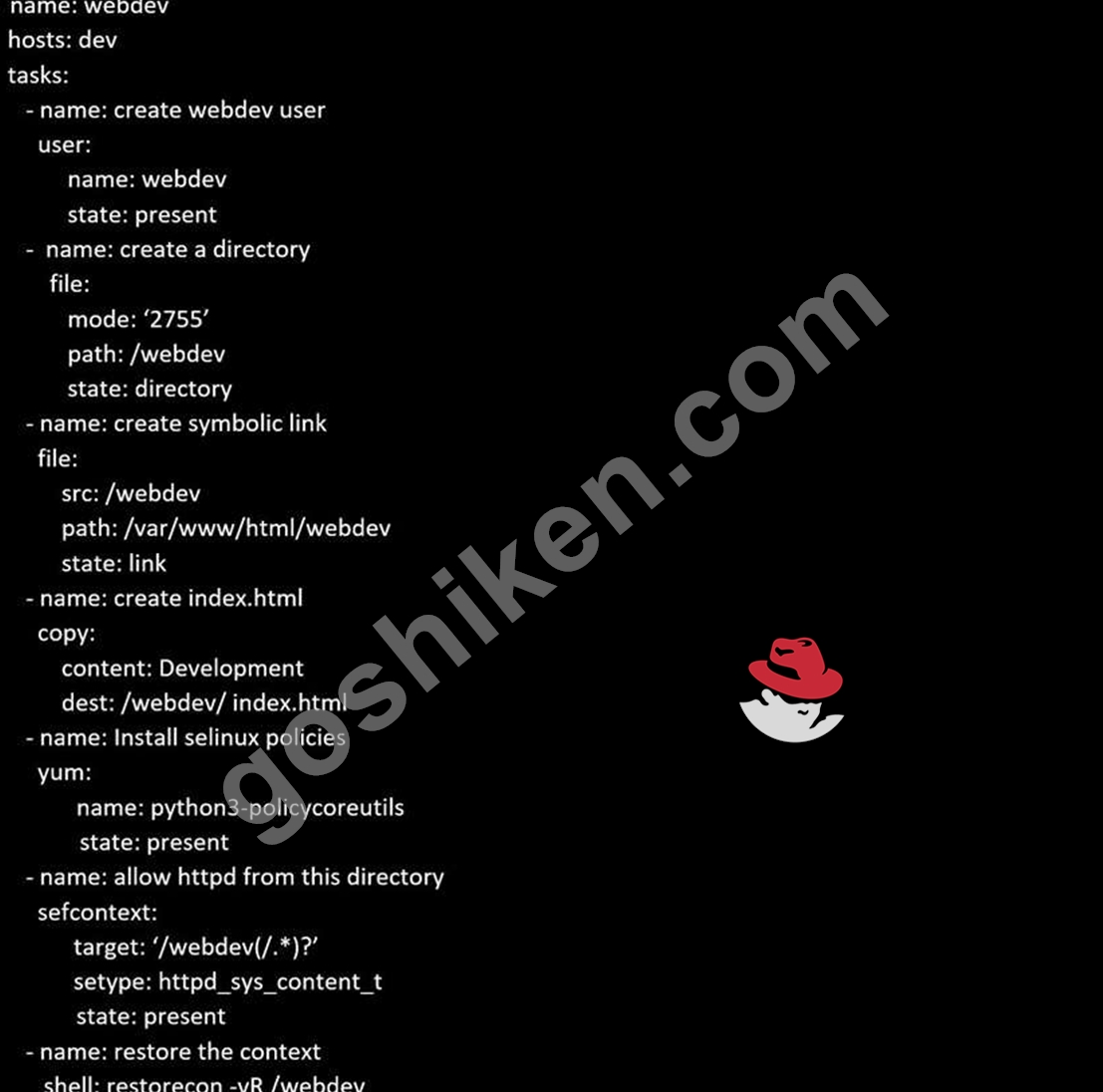
質問 # 28
Create a file called requirements.yml in /home/sandy/ansible/roles a file called role.yml in /home/sandy/ansible/. The haproxy-role should be used on the proxy host. And when you curl http://node3.example.com it should display "Welcome to node4.example.com" and when you curl again "Welcome to node5.example.com" The php-role should be used on the prod host.
- A. Solution as:

Check the proxy host by curl http://node3.example.com - B. Solution as:

Check the proxy host by curl http://node3.example.com
正解:B
質問 # 29
Create an ansible vault password file called lock.yml with the password reallysafepw in the /home/sandy/ansible directory. In the lock.yml file define two variables. One is pw_dev and the password is 'dev' and the other is pw_mgr and the password is 'mgr' Create a regular file called secret.txt which contains the password for lock.yml.
正解:
解説:
ansible-vault create lock.yml
New Vault Password: reallysafepw
Confirm: reallysafepw
質問 # 30
Install and configure ansible
User bob has been created on your control node. Give him the appropriate permissions on the control node. Install the necessary packages to run ansible on the control node.
Create a configuration file /home/bob/ansible/ansible.cfg to meet the following requirements:
* The roles path should include /home/bob/ansible/roles, as well as any other path that may be required for the course of the sample exam.
* The inventory file path is /home/bob/ansible/inventory.
* Ansible should be able to manage 10 hosts at a single time.
* Ansible should connect to all managed nodes using the bob user.
Create an inventory file for the following five nodes:
nodel.example.com
node2.example.com
node3.example.com
node4.example.com
node5.example.com
Configure these nodes to be in an inventory file where node1 is a member of group dev. nodc2 is a member of group test, nodc3 is a member of group proxy, nodc4 and node 5 are members of group prod. Also, prod is a member of group webservers.
正解:
解説:
In/home/sandy/ansible/ansible.cfg
[defaults]
inventory=/home/sandy/ansible/inventory
roles_path=/home/sandy/ansible/roles
remote_user= sandy
host_key_checking=false
[privilegeescalation]
become=true
become_user=root
become_method=sudo
become_ask_pass=false
In /home/sandy/ansible/inventory
[dev]
node 1 .example.com
[test]
node2.example.com
[proxy]
node3 .example.com
[prod]
node4.example.com
node5 .example.com
[webservers:children]
prod
質問 # 31
Generate a hosts file:
* Download an initial template file hosts.j2 from http://classroom.example.com/
hosts.j2 to
/home/admin/ansible/ Complete the template so that it can be used to generate a file with a line for each inventory host in the same format as /etc/hosts:
172.25.250.9 workstation.lab.example.com workstation
* Create a playbook called gen_hosts.yml that uses this template to generate the file /etc/myhosts on hosts in the dev host group.
* When completed, the file /etc/myhosts on hosts in the dev host group should have a line for each managed host:
127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4
::1 localhost localhost.localdomain localhost6 localhost6.localdomain6
172.25.250.10 serevra.lab.example.com servera
172.25.250.11 serevrb.lab.example.com serverb
172.25.250.12 serevrc.lab.example.com serverc
172.25.250.13 serevrd.lab.example.com serverd
-----------------------------------------------------------------
while practising you to create these file hear. But in exam have to download as per questation.
hosts.j2 file consists.
localhost localhost.localdomain localhost4 localhost4.localdomain4
::1
localhost localhost.localdomain localhost6 localhost6.localdomain6
-------------------------------------------------------------------
正解:
解説:
Solution as:
# pwd
/home/admin/ansible
# wget http://classroom.example.com/hosts.j2
# vim hosts.j2
127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4 ::1
localhost localhost.localdomain localhost6 localhost6.localdomain6
{% for host in groups['all'] %}
{{ hostvars[host]['ansible_facts']['default_ipv4']['address'] }} {{ hostvars[host]
['ansible_facts']['fqdn'] }} {{ hostvars[host]['ansible_facts']['hostname'] }}
{% endfor %}
:wq!
# vim gen_hosts.yml
---
- name: collecting all host information
hosts: all
tasks:
- name:
template:
src: hosts.j2
dest: /etc/myhosts
when: inventory_hostname in groups['dev']
:wq
# ansible-playbook gen_hosts.yml --syntax-check
# ansible-playbook gen_hosts.yml
質問 # 32
Create a playbook called balance.yml as follows:
* The playbook contains a play that runs on hosts in balancers host group and uses
the balancer role.
--> This role configures a service to loadbalance webserver requests between hosts
in the webservers host group.curl
--> When implemented, browsing to hosts in the balancers host group (for example
http://node5.example.com) should produce the following output:
Welcome to node3.example.com on 192.168.10.z
--> Reloading the browser should return output from the alternate web server:
Welcome to node4.example.com on 192.168.10.a
* The playbook contains a play that runs on hosts in webservers host group and uses
the phphello role.
--> When implemented, browsing to hosts in the webservers host group with the URL /
hello.php should produce the following output:
Hello PHP World from FQDN
--> where FQDN is the fully qualified domain name of the host. For example,
browsing to http://node3.example.com/hello.php, should produce the following output:
Hello PHP World from node3.example.com
* Similarly, browsing to http://node4.example.com/hello.php, should produce the
following output:
Hello PHP World from node4.example.com
正解:
解説:
Solution as:
# pwd
/home/admin/ansible/
# vim balancer.yml
---
- name: Including phphello role
hosts: webservers
roles:
- ./roles/phphello
- name: Including balancer role
hosts: balancer
roles:
- ./roles/balancer
:wq!
# ansible-playbook balancer.yml --syntax-check
# ansible-playbook balancer.yml
質問 # 33
......
EX294試験に合格することは、候補者がRed Hat Enterprise Linux 8環境で高度なシステム管理タスクを実行するために必要なスキルと知識を持っていることを示しています。この認定は、企業レベルのLinuxシステムを管理および管理する候補者の専門知識を検証する貴重な資格として、世界中の雇用主に認められています。EX294認定は、Linuxシステム管理者、DevOpsエンジニア、およびクラウドインフラストラクチャエンジニアなど、IT業界の多くの求人に必要な前提条件です。
ベストなRedHat EX294学習ガイドと問題集には2023:https://www.goshiken.com/RedHat/EX294-mondaishu.html
